DARPA announced that it has selected three teams for the Mission-Integrated Network Control (MINC) program.
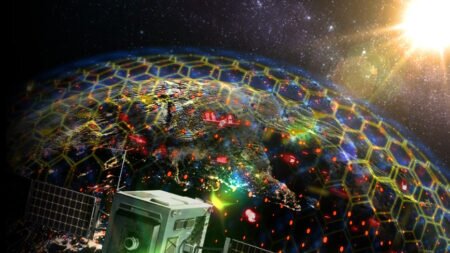
MINC's objective is to ensure that critical data finds a path to the right user at the right time in highly contested, highly dynamic communication environments using secure control of any available communications or networking resources.
The three teams, comprising industry and university researchers, will develop approaches designed to interoperate with a heterogeneous mix of legacy and future systems to ensure timely and reliable delivery of data that is not guaranteed today. This capability will replace the manual, static configuration of individual, tactical networks and the associated limited internetworking capabilities. The growing emphasis on all-domain warfare compounds the complexity of controlling heterogeneous networks. MINC embraces these challenges by introducing the mosaic warfare concepts of optionality, diversity, and rapid adaptability to the orchestration of networks of networks.
The MINC program will realize "on-demand" connectivity to enable effects chains by focusing on the development and integration of three key capabilities. These include creating an "always-on" network overlay to access available networking and communications resources and control parameters; using a cross-network approach for optimizing and managing network configuration and information flows; and creating a mission-driven approach in determining the critical information flows for warfighting services.
“MINC performers are re-imagining the state-of-the-art in commercial networking to develop approaches that will translate mission objectives into network management policies,” said Mary Schurgot, MINC program manager in DARPA’s Strategic Technology Office. “These mission-driven networking approaches will enable self-healing networks to adapt as the mission and operational conditions evolve, while reducing the overall burden on network operators in manually configuring tactical networks.”